CVE-2026-35616 est considérée comme une faille zero-day critique zero-day exploitée, mais ce n'est pas la vulnérabilité elle-même qui mérite le plus d'attention.
Ce qui importe, c'est l'endroit où l'exploit est exécuté et le type de privilèges qu'il confère à un attaquant une fois qu'il a réussi.
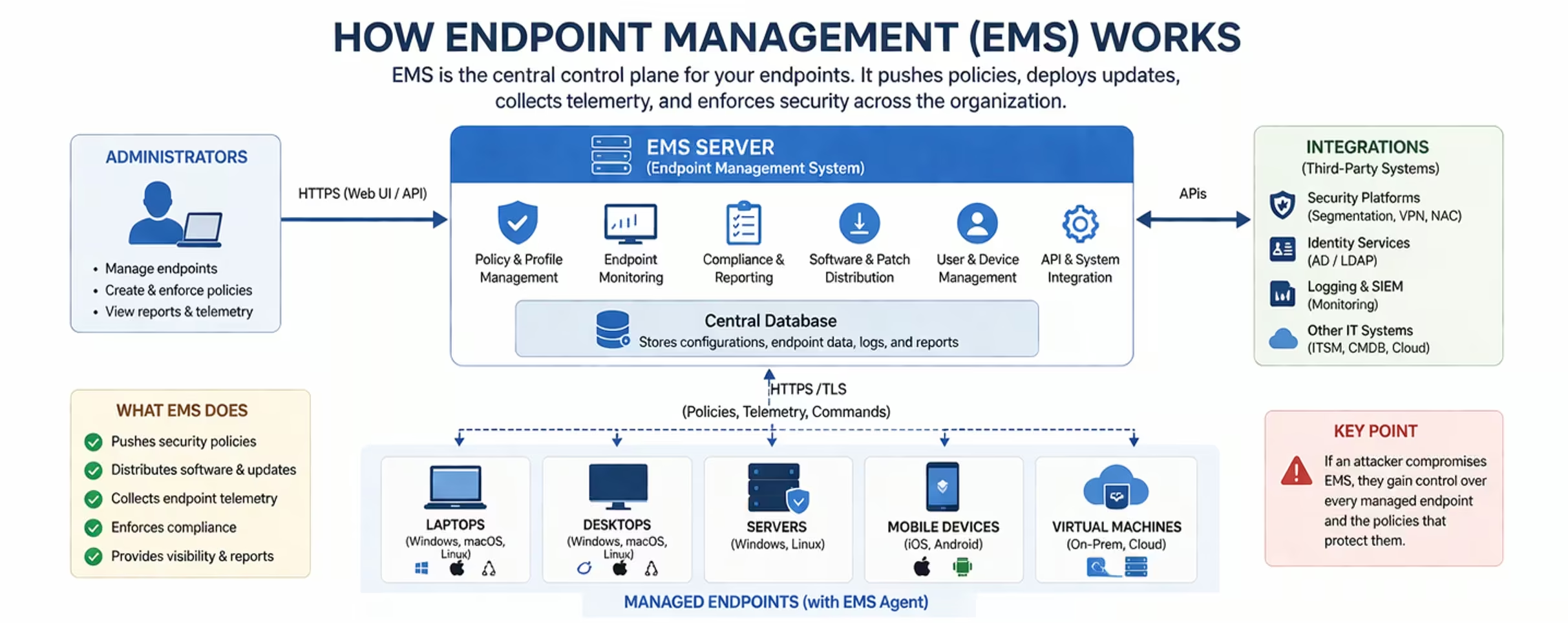
FortiClient EMS n'est pas un simple serveur de plus. Il coordonne les terminaux, distribue les configurations et offre un niveau de fiabilité opérationnelle que la plupart des infrastructures n'ont jamais à justifier. Lorsque ce système est compromis, l'attaquant ne se contente pas d'accéder à un hôte. Il acquiert une portée étendue.
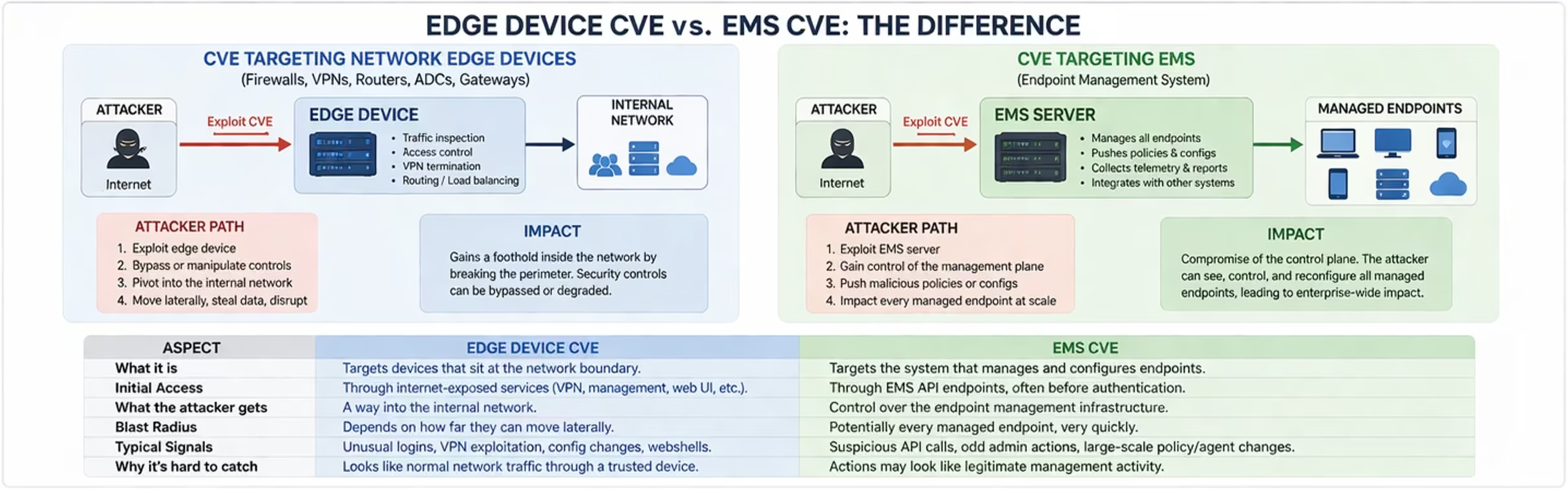
Dans un article précédent consacré aux zero-day » ciblant les périphériques de périphérie réseau, nous avons expliqué comment les attaquants franchissent la périphérie, s'y implantent, puis progressent vers l'intérieur. Ce nouvel exploit montre ce qui se passe lorsque le point de départ se trouve déjà au-delà de cette frontière.
De l'entrée en périphérie à l'accès au plan de contrôle
Le modèle précédent reposait sur une séquence : accéder d'abord à la périphérie, puis se développer.
Dans ce cas, le serveur EMS est souvent suffisamment accessible pour être pris pour cible, tout en étant suffisamment fiable pour que son comportement soit rarement remis en question. La vulnérabilité permet une interaction non authentifiée avec son API, ce qui conduit à l'exécution de code. Cela signifie qu'il n'est pas nécessaire de disposer d'identifiants, que l'intrusion ne dépend pas du comportement de l'utilisateur et qu'elle ne repose pas sur une identité volée au début de l'attaque.
Cela élimine une étape entière du processus d'attaque et repousse la détection à un stade ultérieur.
Il n'y a ni anomalie au niveau des connexions, ni compte suspect, ni comportement utilisateur suspect sur lequel fonder l'enquête. Le pirate informatique accède directement à un système qui dispose déjà d'autorisations sur les terminaux et d'une visibilité sur l'environnement.
Même comportement, contexte différent
Ce comportement n'est pas nouveau. C'est le contexte qui le masque.
Les pirates continuent de cartographier l'environnement, d'identifier les identifiants et de se diriger vers les systèmes les plus sensibles. La différence réside dans la rapidité avec laquelle ils y parviennent et dans le fait que leurs actions semblent tout à fait normales.
Du point de vue d'un système EMS, ces activités se fondent dans le décor. L'extraction endpoint ressemble à une gestion des stocks, la lecture des configurations s'apparente à une tâche administrative, et les connexions internes ressemblent davantage à une gestion courante qu'à un déplacement latéral.
Pourquoi cela est-il difficile à détecter ?
Les indices sont bien là, mais ils ne semblent pas s'imbriquer les uns dans les autres.
L'attaque commence sous la forme d'un trafic API, souvent impossible à distinguer des requêtes habituelles ou du bruit de fond. Au moment où elle aboutit à l'exécution de code, le pirate opère déjà sur un système de confiance.
À partir de là, de petits écarts suffisent : des connexions à de nouveaux systèmes, une authentification valide mais inhabituelle, une activité en dehors des horaires prévus. Chaque signal peut s'expliquer en soi.
La détection échoue car ces signaux sont dispersés entre différents systèmes. L'activité des API est consignée dans les journaux d'application, l'exécution des processus sur l'hôte, les connexions réseau dans des outils distincts et l'authentification dans la surveillance des identités. Aucun signal n'est suffisamment significatif à lui seul.
L'attaquant n'a pas besoin de se cacher. Il mise sur le fait que personne n'observe l'ensemble de la séquence.
À quoi cela ressemble-t-il en télémétrie ?
Ce phénomène s'observe dans divers domaines :
- Activité API sans contexte utilisateur clair
- changements dans le comportement des processus ou des services sur l'hôte EMS
- connexions sortantes vers des systèmes avec lesquels il communique rarement
- une authentification liée aux services plutôt qu'aux utilisateurs
- endpoint hors du cadre habituel
Pris isolément, il s'agit d'événements de faible importance. Ensemble, ils forment une tendance dans laquelle le serveur EMS devient le point de départ endpoint liée à l'identité, au réseau et endpoint .
Concrètement, cela signifie
Si le problème n'est pas détecté à temps, il devient difficile de le maîtriser, car la confiance est en jeu.
En quelques minutes, l'attaquant peut consolider son accès et se faire une idée de l'environnement. À partir de là, il peut se diriger vers les systèmes critiques sans éveiller immédiatement les soupçons. Lorsque l'activité prend clairement un caractère malveillant, l'attaquant dispose déjà d'un contexte et d'un accès qu'il est difficile de démêler.
La réponse ne se limite plus à isoler un seul hôte. Elle nécessite d'examiner les ressources auxquelles ce système a accédé, les modifications qu'il a pu apporter, ainsi que les identifiants ou les relations qui ont pu être compromis.
La détection ne commence plus au niveau de la périphérie. L'accès initial peut ne générer que peu ou pas de signaux exploitables, et les premiers indices fiables n'apparaissent souvent qu'une fois que l'attaquant opère à partir d'un système de confiance.
Cela déplace le problème. La détection consiste alors à identifier les cas où des systèmes dotés de rôles bien définis agissent en dehors de ces rôles, et ce avant que la confiance ne propage l'attaque.
C'est là que la continuité des comportements prend toute son importance. Lorsque le même système devient la source d'activité à travers endpoint de l'identité, du réseau et endpoint , les signaux faibles forment un schéma cohérent.
La Vectra AI s'attaque à ce problème en établissant des liens entre les comportements, l'identité et l'activité réseau, de sorte que les événements de faible intensité forment une image cohérente suffisamment tôt pour permettre une enquête et un confinement.
Si vous souhaitez évaluer dans quelle mesure votre environnement est exposé à ce type de vecteur d'attaque, une évaluation de sécurité offensive peut mettre en évidence les points faibles des systèmes du plan de contrôle et déterminer à quelle vitesse ce type de comportement serait détecté. Dans ce type d'attaque, c'est cette visibilité qui détermine si le serveur EMS génère simplement une alerte de plus ou s'il marque le moment où l'incident est compris.


