La compromission en amont du paquet npm « axios » constitue une étude de cas déterminante en matière d'utilisation malveillante de la chaîne d'approvisionnement. Ces incidents soulignent que l'empoisonnement des dépendances est passé d'un cas théorique marginal à un vecteur d'accès initial très efficace, permettant à des attaquants sophistiqués de parvenir à l'exécution de code à distance (RCE) au sein d'environnements d'entreprise hautement sécurisés.
L'analyse technique indique que les versions compromises d'Axios (v1.14.1 et v0.30.4) ont été infectées par un cheval de Troie afin d'introduire la charge utile malveillante plain-crypto-js@4.2.1. Cet incident marque une rupture majeure par rapport aux risques logiciels traditionnels ; il ne s'agissait pas d'une exploitation d'une vulnérabilité au niveau du code, mais d'un détournement ciblé du processus de publication des paquets.
La plupart des stratégies de sécurité reposent sur l'identification des fonctions vulnérables par le biais d'une analyse statique, mais rares sont celles qui sont conçues pour faire face à un scénario dans lequel le gestionnaire de paquets lui-même sert de vecteur de diffusion à malware dissimulé. Dès que cette dépendance malveillante parvient à s'exécuter en temps réel, la portée de l'incident change immédiatement. Il ne s'agit plus d'une question d'hygiène des dépendances, mais d'un défi de détection post-exploitation visant à comprendre le comportement après l'exécution.
Comment le compromis commence
La télémétrie forensique et l'analyse comportementale ont permis d'établir avec certitude un lien entre l'attaque par empoisonnement d'Axios et Usurpation de compte ATO) visant un responsable de maintenance, ce qui a permis l'injection manuelle d'une dépendance transitive malveillante en contournant les mesures de sécurité traditionnelles des processus CI/CD. Les renseignements actuels attribuent avec un haut degré de certitude cette campagne à BlueNoroff, un groupe de cybercriminels sophistiqué appartenant au Lazarus Group (lié à la RPDC), connu pour ses activités agressives d'exfiltration de données financières et de propriété intellectuelle.
Si l'attribution reste un domaine d'étude en constante évolution, la priorité tactique des équipes de sécurité est claire : une dépendance de confiance est devenue le vecteur d'accès initial. Cet incident met en évidence l'effondrement de la confiance implicite dans l'écosystème open source. Pour les organisations gérant une infrastructure CI/CD ou des environnements de build cloud, cela marque un changement crucial dans la surface d'attaque : les workflows standard des développeurs ne sont plus des zones sûres « pré-authentifiées », mais des cibles de grande valeur pour le déploiement de chevaux de Troie d'accès à distance (RAT) commandités par des États.
: Comment l'enquête doit évoluer
Les modèles de sécurité traditionnels reposent en grande partie sur des évaluations des risques centrées sur les CVE, qui accordent la priorité à l'identification des vulnérabilités latentes au sein du code source. Cependant, ces modèles ne tiennent pas compte de l'utilisation malveillante du canal de distribution, dans lequel le gestionnaire de paquets passe du statut d'utilitaire administratif fiable à celui de principal vecteur malware .
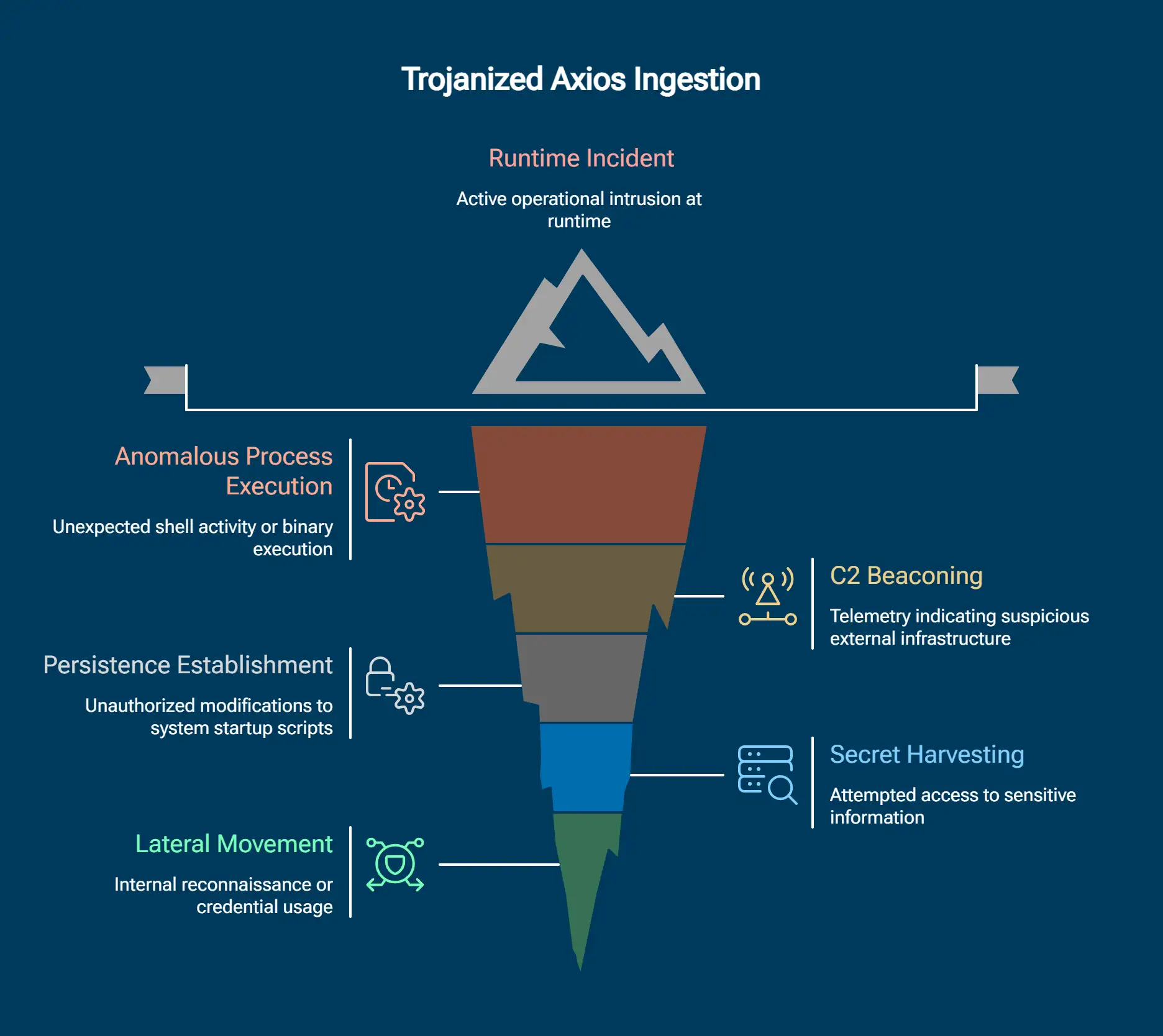
Au moment de l'exécution, l'incident passe d'un simple problème de sécurité des dépendances à une intrusion opérationnelle active. Si un poste de travail de développeur, un outil de compilation ou un pipeline de déploiement a intégré une version d'Axios infectée par un cheval de Troie, l'enquête doit immédiatement aller au-delà d'une simple suppression. Une recherche efficace des menaces après exécution doit porter sur :
- Exécution anormale d'un processus : le processus npm ou node a-t-il déclenché une activité shell inattendue ou l'exécution d'un binaire (par exemple, cmd.exe, /bin/sh) ?
- C2 Beaconing : Existe-t-il des données télémétriques indiquant des sorties vers des infrastructures externes non standard ou suspectes ?
- Vérification de la persistance : des modifications non autorisées ont-elles été apportées aux scripts de démarrage du système, aux tâches cron ou aux clés de registre ?
- Collecte clandestine : a-t-on tenté d'accéder à des variables d'environnement, à des identifiants ou à des trousseaux locaux ?
- Mouvement latéral : existe-t-il des indices laissant supposer une reconnaissance interne ou une utilisation d'identifiants provenant du serveur de compilation concerné ?
C'est là que réside la faille majeure des systèmes de détection modernes : considérer les compromissions de la chaîne logistique comme de simples « problèmes de paquets » isolés plutôt que comme des têtes de pont bien établies. Pour dissuader les acteurs sophistiqués, les défenseurs doivent opérer dans le cadre d'une Zero Trust » qui traite chaque dépendance malveillante comme une violation à grande échelle du réseau.
Si tu ne m'écoutes toujours pas
Une fois l'exécution réussie, l'attaquant ne dépend plus du paquet, mais des droits d'accès dont il dispose dans l'environnement.
Et si l'hypothèse selon laquelle BlueNoroff serait à l'origine de ces faits se confirme, l'exfiltration initiale des secrets CI/CD, des clés cloud et des dépôts de code source n'est que le prélude à une réorientation opérationnelle aux conséquences considérables.
La compromission des identifiants de niveau développeur permet en effet de contourner la barrière physique de l'environnement de production, transformant ainsi l'infection d'un poste de travail local en une intrusion dans le plan cloud . Entre les mains d'un acteur soutenu par un État, cette exfiltration conduit directement à :
- Exploitation des secrets volés : la transformation rapide en armes des clés Cloud et des secrets Kubernetes récupérés afin d'établir une présence persistante dotée de privilèges élevés au sein de l'infrastructure.
- Supply Chain secondaire : utilisation de certificats de signature de code volés ou d'un accès en écriture au référentiel pour injecter du code malveillant supplémentaire dans les produits destinés aux clients de l'entreprise, élargissant ainsi la portée de l'attaque à l'ensemble de sa base d'utilisateurs.
- Expansion latérale via des identifiants : passage de l'écosystème des développeurs vers des bases de données de production ou des systèmes financiers hautement sensibles. Comme l'attaquant utilise des identifiants légitimes qu'il a récupérés, il peut contourner les mesures de sécurité traditionnelles basées sur les signatures, ce qui fait des analyses comportementales la seule méthode viable pour détecter l'intrusion.
À quoi ressemble la faille Axios sur le réseau
Dans le cadre d'une attaque de la chaîne logistique, comme celle qui a touché Axios, les journaux au niveau de l'hôte sont souvent effacés ou contournés par des binaires « de confiance ». La « Network Truth » reste le seul enregistrement immuable des intentions tactiques de l'intrus.
Les comportements suivants, observés « en temps réel », révèlent la nature de l'attaque au fur et à mesure qu'elle passe d'une simple installation de paquet à une intrusion aux conséquences graves :
- Anomalies au niveau du rythme et du protocole C2 : détecte le rythme « lent et régulier » des communications Command & Control C2) dissimulées dans le protocole HTTPS.
- Préparation malveillante (sortie sortante) : signale le moment précis où le processus d'installation récupère une charge utile de deuxième phase.
- Reconnaissance interne (trafic est-ouest) : détecte les « traces » laissées par l'intrus qui cartographie votre environnement sur le réseau bien avant que l'attaquant ne tente sa première exploitation interne.
- Anomalies liées aux accès privilégiés : identifie les attaques basées sur l'identité en cours de transmission. Le système détecte les requêtes anormales ou les premières authentifications sur les systèmes de production effectuées à l'aide d'identifiants de développeurs piratés.
- Contrefaçon et acheminement clandestin de données : surveille les exfiltrations en temps réel. Le système signale le « fractionnement » de données au sein de tunnels cryptés ou les requêtes DNS anormales utilisées pour faire sortir clandestinement du réseau des secrets d'environnement et cloud .
Ce n'est plus un problème de périmètre
L'incident Axios est bien plus qu'une simple défaillance de la chaîne d'approvisionnement ; c'est un signal d'alarme concernant l'effondrement du périmètre de sécurité traditionnel. Depuis trop longtemps, l'infrastructure des développeurs constitue un « angle mort » en matière de sécurité : isolée des principales stratégies de détection, elle offre une voie d'accès facile aux acteurs sophistiqués tels que BlueNoroff.
Pour garder une longueur d'avance sur les groupes soutenus par des États, les défenseurs doivent abandonner la « norme » consistant à se concentrer uniquement sur l'environnement de production et adopter une approche qui considère l'ensemble du cycle de vie des logiciels comme une surface d'attaque unifiée.
La question n'est plus : « Un paquet malveillant s'est-il introduit dans notre environnement ? » La question est désormais : « Notre visibilité s'étend-elle suffisamment en profondeur dans notre écosystème de développement pour repérer l'intrus avant qu'il ne s'attaque à nos joyaux de la couronne en production ? » En adoptant cette nouvelle approche, on transforme une vulnérabilité systémique en un avantage défensif maîtrisé, garantissant ainsi qu'aucune partie de l'infrastructure ne se trouve hors du champ de protection de détection et réponse aux incidents de détection et réponse aux incidents
Si votre équipe cherche à repenser la manière de détecter les comportements malveillants au-delà de l'analyse des paquets et des contrôles préventifs, c'est exactement là qu'intervient Vectra AI peut vous aider à mettre en évidence les activités suspectes post-compromission dans les environnements cloud, d'identité et en réseau.

.jpg)