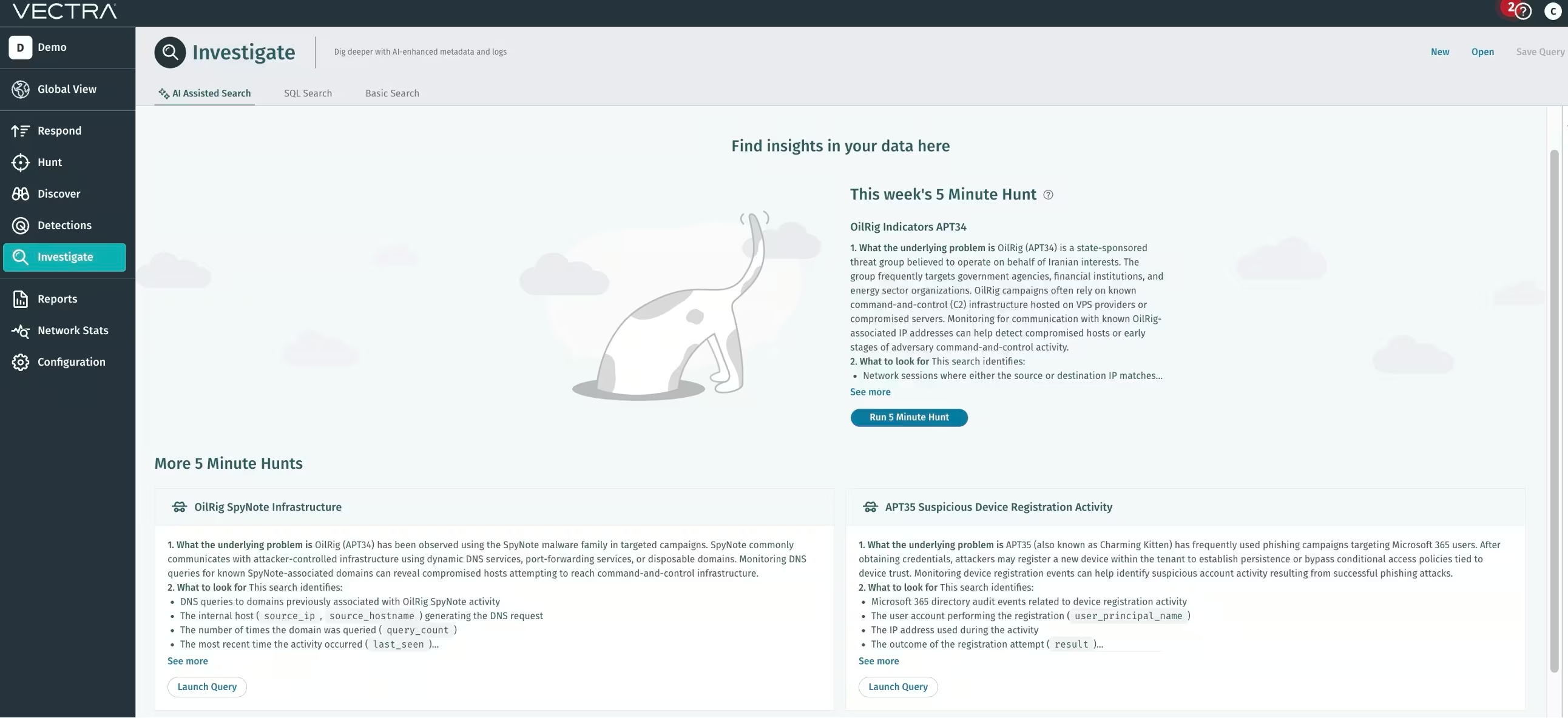
À propos de la « 5-Minute Hunt » : La « 5-Minute Hunt » est une fonctionnalité disponible dans l'application Vectra AI plateforme , sous l'onglet « Investigate ». Chaque chasse met en évidence un comportement spécifique d'un attaquant et fournit une requête prête à l'emploi que vous pouvez utiliser immédiatement.
Les analyses de cette semaine portent sur des groupes malveillants liés à l'État iranien, notamment OilRig (APT34) et Charming Kitten (APT35), qui continuent de cibler des organisations en exploitant des identités compromises et en utilisant des infrastructures de commande et de contrôle dissimulées.
Les groupes affiliés à l'Iran s'appuient rarement sur un seul point d'entrée. Une chaîne d'intrusion type commence par phishing visant les identifiants phishing par une attaque de « password spraying », suivie d'une persistance discrète dans les systèmes cloud et de communications sortantes vers l'infrastructure des attaquants. Le trafic réseau et les journaux d'identité SaaS contiennent souvent les premières traces de ces activités.
Les sessions de recherche de 5 minutes suivantes sont conçues pour mettre rapidement en évidence ces signaux au sein de Vectra AI plateforme.
À la recherche d'APT35 – Charming Kitten
Malware Pupy d'APT35
On a constaté que le groupe APT35 utilisait l'outil d'administration à distance Pupy dans le cadre de campagnes d'espionnage ciblées.
Pupy est unplateforme qui permet aux pirates de contrôler à distance les hôtes compromis, d'exécuter des commandes et d'exfiltrer des données sensibles. Une fois déployé, les systèmes infectés communiquent avec des serveurs de commande et de contrôle externes pour recevoir des instructions et transmettre les informations collectées.
La surveillance des communications avec l'infrastructure connue de Pupy peut permettre d'identifier les systèmes compromis dès les premières phases de l'attaque.
Objectif de la requête
Cette recherche identifie :
- Sessions réseau dans lesquelles l'adresse IP source ou destination correspond à une infrastructure connue associée aux activités du groupe APT35 Pupy
- Le protocole utilisé pour la communication
(proto_name) - Le nombre de connexions entre les hôtes
(nombre_de_connexions) - La dernière fois que cette activité a été observée
(dernière connexion)
SELECT
id.orig_h AS source_ip,
id.resp_h AS dest_ip,
proto_name,
COUNT(*) AS nombre_de_connexions,
MAX(timestamp) AS dernière_apparition
FROM network.isession._all
WHERE
(id.orig_h IN ('154.12.20.218', '144.172.107.157', '149.28.52.61', « 66.55.159.84 », « 172.235.235.80 »)
OU id.resp_h DANS ('154.12.20.218', '144.172.107.157', '149.28.52.61', « 66.55.159.84 », « 172.235.235.80 »))
ET horodatage ENTRE date_add('day', -14, now()) ET now()
GROUP BY id.orig_h, id.resp_h, proto_name
ORDER BY connection_count DESC
LIMIT 100
Ce qu'il faut rechercher
Les analystes devraient accorder une attention particulière aux points suivants :
- Des hôtes internes communiquant de manière répétée avec la même adresse IP externe suspecte
- Connexions établies via des protocoles inattendus pour le système
- Connexions persistantes ou récurrentes pouvant indiquer un comportement de balisage
Comment approfondir la recherche
- Vérifier les adresses IP suspectes à l'aide de sources de renseignements sur les menaces et de listes d'autorisation internes
- Exploitez les données DNS, HTTP, SSL et endpoint pour identifier les activités associées
- Analyser les processus de l'hôte à l'origine du trafic réseau à l'aide d'EDR ou de Sysmon
- Si la nature malveillante est confirmée, bloquez l'infrastructure et isolez le endpoint concerné endpoint la correction
Techniques MITRE associées :
- T1071 – Protocole de la couche application
- T1105 – Transfert d'outils d'entrée
- T1059 – Interpréteur de commandes et de scripts
Échec de l'enregistrement d'un appareil lié aux activités de reconnaissance d'APT35
APT35 mène souvent des opérations de reconnaissance au sein des environnements Microsoft 365 après avoir récupéré des identifiants.
Une technique courante consiste à tenter d'enregistrer de nouveaux appareils sur des comptes utilisateur. Lorsque ces tentatives échouent, cette activité peut néanmoins fournir des indices précieux indiquant qu'un attaquant teste des identifiants ou examine les politiques des locataires avant de tenter de s'implanter durablement.
Des tentatives répétées d'enregistrement d'appareils qui échouent peuvent indiquer que des pirates testent des identifiants volés ou étudient les politiques de confiance des appareils avant de lancer une intrusion plus ciblée.
Objectif de la requête
Cette recherche identifie :
- Événements d'audit du répertoire Microsoft 365 liés à des tentatives d'enregistrement d'appareils ayant échoué
- Le compte utilisateur à l'origine de la tentative
(user_principal_name) - L'adresse IP d'origine
- La cause de la panne
(motif_du_résultat) - Ressources associées impliquées dans la tentative d'enregistrement
SELECT
id,
date_heure_activité,
nom_d'affichage_de_l'activité,
initiated_by.user.user_principal_name,
initiated_by.user.ip_address,
résultat,
motif_du_résultat,
ressources_cibles
FROM m365.directory_audits._all
WHERE
LOWER(nom_d'affichage_de_l'activité) LIKE '%enregistrer un appareil%'
AND LOWER(result) = 'failure'
ET timestamp > date_add('day', -14, DATE(NOW()))
ORDER BY date_heure_activité DESC
LIMIT 100
Ce qu'il faut rechercher
Les analystes devraient accorder une attention particulière aux points suivants :
- Plusieurs tentatives infructueuses provenant de la même adresse IP
- Tentatives visant plusieurs utilisateurs au sein du tenant
- Échecs d'enregistrement d'appareils provenant de zones géographiques inconnues
- Activité survenant peu après des tentatives de connexion suspectes ou phishing
Comment approfondir la recherche
- Consultez les journaux de connexion et les événements d'authentification associés au compte utilisateur
- Vérifier si l'adresse IP est associée à des VPN, à des services d'anonymisation ou à une infrastructure connue d'attaquants
- Vérifier si les tentatives suivantes d'authentification ou d'enregistrement de l'appareil ont abouti
- Si une activité suspecte est confirmée, imposez la réinitialisation des mots de passe, mettez fin aux sessions et surveillez le compte afin de détecter tout autre comportement anormal
Techniques MITRE associées :
- T1078.004 – Comptes valides (Cloud )
- T1595 – Balayage actif
- T1598 – Phishing des informations
Enregistrement d'un appareil suspect lié à une attaque Phishing d'APT35
APT35, souvent surnommé « Charming Kitten », est connu pour ses campagnes de collecte d'identifiants ciblant les utilisateurs de Microsoft 365. Une fois qu'ils ont obtenu des identifiants valides, les attaquants enregistrent souvent un nouvel appareil au sein du tenant.
Cette tactique leur permet de conserver leur accès même en cas de changement de mot de passe et peut contourner les règles d'accès conditionnel liées aux appareils de confiance. Concrètement, elle permet à l'attaquant d'agir comme un endpoint légitime endpoint l'environnement.
Les événements liés à l'enregistrement des appareils sont consignés dans les journaux d'audit de l'annuaire Microsoft 365, ce qui en fait un indicateur précieux lors de la recherche dephishing .
Objectif de la requête
Cette recherche identifie :
- Événements d'audit du répertoire Microsoft 365 liés à l'enregistrement des appareils
- Le compte utilisateur qui effectue l'inscription
(user_principal_name) - L'adresse IP utilisée pendant l'activité
- Résultat de la tentative d'inscription
(résultat) - Ressources associées impliquées dans l'action
(ressources_cibles)
SELECT
id,
date_heure_activité,
nom_d'affichage_de_l'activité,
initiated_by.user.user_principal_name,
initiated_by.user.ip_address,
résultat,
ressources_cibles
FROM m365.directory_audits._all
WHERE
LOWER(nom_d'affichage_de_l'activité) LIKE '%register device%'
AND timestamp > date_add('day', -14, DATE(NOW()))
ORDER BY date_heure_activité DESC
LIMIT 100
Ce qu'il faut rechercher dans les résultats
Les analystes devraient accorder une attention particulière aux points suivants :
- Enregistrements d'appareils provenant d'adresses IP inconnues ou étrangères
- Inscriptions effectuées peu après des connexions suspectes
- Comptes qui n'ont jamais enregistré d'appareils auparavant
- Enregistrement de plusieurs appareils en peu de temps
Comment approfondir l'enquête
- Vérifiez si l'appareil appartient bien à son propriétaire légitime.
- Croisez ces données avec les journaux de connexion à Microsoft 365 et les alertes de connexion à risque.
- Recherchez d'autres événements liés à la gestion des identités, tels que de nouvelles méthodes d'authentification, des réinitialisations de mot de passe ou la création de jetons.
- Si l'activité semble malveillante, révoquez les sessions, réinitialisez les identifiants et supprimez les appareils non autorisés du tenant.
Techniques MITRE associées :
- T1078.004 – Comptes valides (Cloud )
- T1098 – Manipulation de compte
Sur les traces d'APT34 – OilRig
Détection de l'infrastructure de commande et de contrôle d'OilRig (APT34)
OilRig, également connu sous le nom d'APT34, mène régulièrement des campagnes d'espionnage de longue haleine visant des organismes gouvernementaux, financiers et énergétiques.
Une caractéristique récurrente de ces campagnes est la communication constante avec des infrastructures contrôlées par les pirates, hébergées sur des serveurs compromis ou chez des fournisseurs de serveurs virtuels privés (VPS) à bas prix.
Même lorsque malware fortement dissimulés, l'infrastructure utilisée pour le commandement et le contrôle a tendance à rester active suffisamment longtemps pour permettre de détecter les schémas de communication réseau.
La surveillance du trafic vers les infrastructures OilRig connues permet de détecter rapidement les hôtes compromis ou les systèmes de préparation utilisés lors des premières phases d'une attaque.
Objectif de la requête
Cette recherche identifie :
- Sessions réseau dans lesquelles l'adresse IP source ou destination correspond à une infrastructure OilRig connue
- Le protocole utilisé pour la communication
(proto_name) - Le nombre total de connexions entre les hôtes
- La dernière fois que cette activité a été observée
(dernière connexion)
SELECT
id.orig_h AS source_ip,
id.resp_h AS dest_ip,
proto_name,
COUNT(*) AS nombre_de_connexions,
MAX(timestamp) AS dernière_apparition
FROM network.isession._all
WHERE
(id.orig_h IN ('103.61.224.102', '178.209.51.61', '185.76.78.177')
OU id.resp_h DANS ('103.61.224.102', '178.209.51.61', '185.76.78.177'))
ET horodatage ENTRE date_add('day', -14, now()) ET now()
GROUP BY id.orig_h, id.resp_h, proto_name
ORDER BY connection_count DESC
LIMIT 100
Ce qu'il faut rechercher
Les analystes devraient accorder une attention particulière aux points suivants :
- Des hôtes internes qui contactent à plusieurs reprises la même adresse IP suspecte
- Connexions établies via des protocoles inhabituels ou inattendus
- Des schémas de communication persistants suggérant un comportement de balisage
Comment approfondir la recherche
- Vérifier les adresses IP suspectes à l'aide des flux de renseignements sur les menaces et des rapports récents concernant l'infrastructure OilRig
- Examinez les données DNS, HTTP, SSL et endpoint pour l'hôte concerné
- Examinez les journaux d'exécution du processus afin d'identifier malware les scripts à l'origine de ces connexions
- Bloquer les infrastructures malveillantes identifiées au niveau des contrôles périmétriques et isoler les hôtes compromis en vue de leur remédiation
Techniques MITRE associées :
- T1071 – Protocole de la couche application
- T1105 – Transfert d'outils d'entrée
- T1090 – Mandataire
Activité de l'infrastructure OilRig SpyNote
On a constaté que des campagnes OilRig déployaient la malware SpyNote.
SpyNote communique fréquemment avec l'infrastructure des pirates hébergée derrière des services DNS dynamiques ou des plateformes de redirection de ports. Ces domaines changent souvent rapidement, mais suivent des schémas reconnaissables liés à des services tels que localto.net ou portmap.host.
Même lorsque le malware inactif, les hôtes infectés ont tendance à effectuer des requêtes DNS répétées vers ces domaines tout en essayant de se reconnecter aux serveurs de commande et de contrôle.
Ces requêtes DNS peuvent révéler l'existence de systèmes infectés avant même que le pirate n'émette activement des commandes.
Objectif de la requête
Cette recherche identifie :
- Requêtes DNS vers des domaines précédemment associés à l'activité d'OilRig SpyNote
- L'hôte interne
(adresse_IP_source, nom_d'hôte_source)générer la requête DNS - Nombre de fois où le domaine a été interrogé
(nombre_de_requêtes) - La dernière fois que cette activité a eu lieu
(dernière connexion)
SELECT
query AS queried_domain,
id.orig_h AS source_ip,
orig_hostname.name AS nom_hôte_source,
COUNT(*) AS nombre_de_requêtes,
MAX(timestamp) AS dernière_apparition
FROM network.dns._all
WHERE
query IN (
'hecker12345-61516.portmap.host',
'software-garlic.gl.at.ply.gg',
'dohinukss.localto.net',
« suzrbgndb.localto.net »,
« 49lwbineu.localto.net »,
« idi-nahuy.net »,
« utoigzdol.localto.net »,
« cyqahoxnt.localto.net »,
« xnd4x3ezm.localto.net »,
« 5z6y8mkfe.localto.net »,
« fqq121qq-33728.portmap.host »,
« shabi9988-64207.portmap.host »,
« shzkagxdv.localto.net »,
« artemmakarov-30233.portmap.host »,
« hssshsh-33054.portmap.host »,
« 0p7wfcoia.localto.net »,
« wq4x0gt8l.localto.net »,
« cezamail.com.cezamail.com »,
« cezamail.com.localto.net »,
« buglwf041.lo »
)
ET horodatage COMPRIS ENTRE date_add('day', -14, now()) ET now()
GROUP BY query, id.orig_h, orig_hostname.name
ORDER BY query_count DESC
LIMIT 100
Ce qu'il faut rechercher
Les analystes devraient accorder une attention particulière aux points suivants :
- Des serveurs qui interrogent sans cesse le même domaine suspect
- Requêtes adressées à une infrastructure DNS dynamique telle que
localto.netouportmap.host - Requêtes survenant peu après l'exécution d'un processus suspect ou une activité suspecte de l'utilisateur
Comment approfondir la recherche
- Analyser l'hôte à l'origine des requêtes à l'aide de endpoint (EDR, Sysmon, etc.)
- Examinez les sessions HTTP/SSL pour déterminer si des connexions ultérieures ont eu lieu
- Vérifier la conformité des domaines par rapport aux flux de renseignements sur les menaces et aux rapports de sandbox
- Si une activité malveillante est confirmée, isolez l'hôte, bloquez les domaines et procédez à une remédiation complète
Techniques MITRE associées :
- T1071.004 – Protocole de la couche application (DNS)
- T1105 – Transfert d'outils d'entrée
- T1090 – Mandataire
Recherche d'activité liée à l'infrastructure de QasarRAT
QasarRAT est un cheval de Troie d'accès à distance open source largement utilisé, fréquemment employé dans le cadre de campagnes d'espionnage et de surveillance. Une fois déployé, il confère aux attaquants un contrôle permanent sur les systèmes compromis, leur permettant d'exécuter des commandes, de surveiller l'activité et d'exfiltrer des données.
De nombreuses campagnes QasarRAT s'appuient sur des fournisseurs de DNS dynamique pour héberger leur infrastructure de commande et de contrôle. Ces services permettent aux pirates de changer régulièrement de serveurs backend tout en conservant le même nom de domaine actif, ce qui rend l'infrastructure plus difficile à tracer.
Même lorsque le malware inactif, les systèmes infectés continuent généralement d'effectuer des résolutions vers le domaine C2. La surveillance des requêtes DNS liées à l'infrastructure connue de QasarRAT peut permettre de détecter les hôtes compromis qui tentent d'accéder à des serveurs contrôlés par les attaquants.
Objectif de la requête
Cette recherche identifie :
- Requêtes DNS vers des domaines précédemment observés dans l'infrastructure de QasarRAT
- Hôtes internes
(adresse_IP_source, nom_d'hôte_source)exécuter les requêtes - Fréquence des demandes
(nombre_de_requêtes) - La dernière fois que cette activité a été observée
(dernière connexion)
SELECT
query AS queried_domain,
id.orig_h AS source_ip,
orig_hostname.name AS nom_hôte_source,
COUNT(*) AS nombre_de_requêtes,
MAX(timestamp) AS dernière_apparition
FROM network.dns._all
WHERE
query IN (
'luvxcide.duckdns.org',
'projectindia999.loseyourip.com',
'cia.anondns.net',
« skittlesforlife.anondns.net »,
« bnli8khzo.localto.net »,
« isof63umlw.loclx.io »,
« docsc.ddns.net »
)
ET horodatage COMPRIS ENTRE date_add('day', -14, now()) ET now()
GROUP BY query, id.orig_h, orig_hostname.name
ORDER BY query_count DESC
LIMIT 100
Ce qu'il faut rechercher
Les analystes devraient accorder une attention particulière aux points suivants :
- Des serveurs qui interrogent sans cesse le même domaine suspect
- Domaines hébergés chez des fournisseurs de DNS dynamique (par exemple : duckdns.org, ddns.net, anondns.net, localto.net, loclx.io)
- Activité DNS coïncidant avec l'exécution d'un processus suspect ou un trafic sortant inattendu
Comment approfondir la recherche
- Analyser l'hôte d'origine à l'aide de endpoint (EDR, Sysmon, etc.) afin d'identifier les processus à l'origine des requêtes
- Examiner les données de session réseau (isession, SSL, HTTP) afin de déterminer si les connexions ont été établies après la résolution DNS
- Vérifier la conformité des domaines par rapport aux sources de renseignements sur les menaces et malware
- Si la nature malveillante est confirmée, bloquez les domaines et isolez le système concerné en vue d'une correction
Techniques MITRE associées :
- T1071.004 – Protocole de la couche application (DNS)
- T1105 – Transfert d'outils d'entrée
- T1059 – Interpréteur de commandes et de scripts
Réflexions finales
cybercriminels liés à l'Iran cybercriminels largement sur l'utilisation abusive d'identifiants, la manipulation cloud et des canaux de commande et de contrôle clandestins. Bon nombre de ces activités se fondent dans le trafic légitime et le comportement des utilisateurs, ce qui les rend difficiles à détecter à l'aide des seules défenses périmétriques traditionnelles.
La mise en place de recherches ciblées de ce type permet aux analystes de détecter des indicateurs précoces avant que les attaquants n'étendent leurs privilèges, ne préparent des données ou ne s'enfoncent plus profondément dans l'environnement.
Si vous utilisez déjà le Vectra AI plateforme, vous pouvez exécuter ces requêtes directement dans l'onglet « Investigate » et basculer immédiatement vers les données de télémétrie d'identité et de réseau afin de déterminer si l'activité est bénigne ou malveillante.
De nouvelles « chasses » de 5 minutes sont régulièrement mises à disposition pour aider les équipes SOC à identifier plus rapidement les comportements des attaquants et à réduire le délai entre l'intrusion et la réponse.
Vous n'êtes pas encore client ? Découvrez nos démonstrations en libre-service pour découvrir comment la détection comportementale met automatiquement en évidence ces menaces.